In today’s digital world, every system and application faces constant cyber risks. To stay safe organisations needs a clear way to understand what could go wrong before an attack happens. This is where Threat Modelling becomes important. It is a step-by-step method that helps identify what needs protection, how the system works, and where possible weaknesses may exist. Threat Modelling guides teams through simple but effective stages-from listing important assets to spotting threats, understanding their impact and planning the right security controls. With well-known methods like STRIDE, PASTA, VAST, SQUARE and OCTAVE, businesses can choose the approach that fits their system best.
As cybersecurity threats keep growing, Threat Modelling has become essential for building secure applications from the start. It helps reduce risks early, improves decision-making and strengthens overall security. By using Threat Modelling at the right time, Organizations can create systems that are safer, smarter, and more prepared for modern cyber challenges.
Table of Contents
What is Threat Modeling?
Threat Modeling is a structured security exercise called threat modeling that is used to find, evaluate, and fix possible weaknesses in an application, system, or infrastructure. It involves creating a detailed representation of the system’s components, data flows, and interactions to identify potential vulnerabilities that an attacker can exploit. In simple terms threat modeling is similar to looking at an application’s blueprints to identify potential security flaws. Security experts and developers examine a building’s layout to identify blind spots and entry points. This method works best when used at every level of the software development lifecycle (SDLC), particularly in the planning and design phases, rather than after deployment. It helps teams in anticipating possible risks, setting priorities for mitigation techniques, and strengthening the system’s defenses before attackers can take advantage of them.
what-is-a-zero-day-exploit-explained
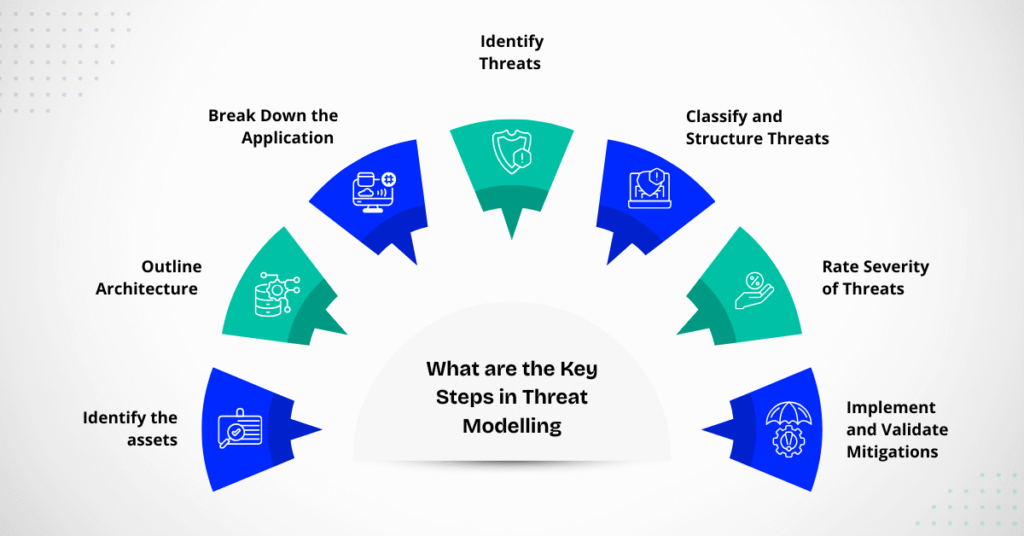
What are the key Steps in Threat Modeling?
1. Identify the assets
The first step in Threat modeling is to identify what you are trying to protect the assets. Data (such as financial records, customer information, or intellectual property), system parts, software, and even business processes can all be considered assets. Understanding what’s valuable helps prioritise where to focus security efforts. For example, compared to temporary log files, a company’s user database can be a high-value target. During this stage, it’s crucial to define both tangible and intangible assets—from physical devices to digital credentials. The basis for evaluating threats and coordinating security measures to safeguard what really counts is established by accurate asset identification.
2. Outline Architecture
Once assets are known the next step is to outline the application’s or system’s architecture. This involves creating a clear diagram of how the system works, including servers, databases, APIs, data flows, and external connections. The architecture diagram helps visualize entry points, trust boundaries, and communication channels. For example, knowing how a web server interacts with a database or third-party API might show where sensitive data travels and how it can be intercepted. A well-documented architecture serves as a visual blueprint that helps developers and security experts see the system from an attacker’s point of view, which makes it simpler to identify vulnerabilities early in the design process.
3. Break Down the Application
Breaking Down the Application means, diving deeper into how each component functions. This includes data validation, user authentication, input and output management, and module logic analysis. Each part of the system should be examined for potential weaknesses, such as unencrypted communication, poor session management, or insecure APIs. . Security teams can gain a better understanding of how data is moved, stored, and processed by breaking the application into smaller parts. Because of this granular view, developers can plan security procedures that safeguard every layer of the program and ensure that no element, no matter how small, is neglected.
4. Identify Threats
At this stage, the focus shifts to identifying potential threats that could exploit weaknesses in the system. Common threat categories include Unauthorized access, data breaches, denial of service, and malware attacks. Frameworks such as STRIDE (Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, and Elevation of Privilege) help systematically discover threats in different parts of the application. Teams brainstorm scenarios “what could go wrong,” and how an attacker might achieve it. The goal is to list out every realistic threat-whether it comes from external hackers, insider misuse or system misconfiguration- ensuring no potential risk is ignored.
5. Classify and Structure Threats
After identifying potential threats, it’s essential to classify and arrange them according to their kind, origin, and potential consequences. Threat classification helps teams organise vulnerabilities into meaningful categories, making it easier to analyze and respond.
Structured Frameworks like CVSS (Common Vulnerability Scoring System) or DREAD (Damage, Reproducibility, Exploitability, Affected Users, Discoverability) are often used to measure how severe a threat is . Grouping threats allows security professionals to visualise attack paths, Security experts can see attack vectors, understand dependencies, and make sure that mitigation efforts are consistent and properly prioritized by grouping threats.
6. Rate Severity of Threats
Not all threats carry the same level of risk, so the next step is to evaluate and rank them by severity. This involves assessing how damaging a particular threat could be, how likely it is to occur, and what assets it impacts. High-severity threats, such as those compromising sensitive data or crucial services should be addressed immediately. Rating systems like high, medium low help the team prioritise mitigation efforts and allocate resources efficiently. This process ensures that the most dangerous and probable threats are neutralised first, improving both the application’s resilience and the organisation’s overall security posture.
7. Implement and Validate Mitigations
The final step is to implement security controls and verify that they effectively mitigate the identified threats. This can include redesigning unsafe components, adding access controls, patching vulnerabilities, and implementing encryption are some examples of how to do things. Once these measures are applied, Validation tests, such as penetration testing, code reviews, or security audits, are conducted to confirm that the threats have been properly addressed. Continuous monitoring is essential, as new vulnerabilities can emerge with updates or environment changes. This step completes the modeling cycle, ensuring the application remains secure and that defences evolve alongside potential threats.
10-crucial-ways-to-guard-against-phishing-attacks
Different Methods of Threat Modeling
A Threat Modeling Methodology is a structured approach that guides security professionals in identifying, evaluating and mitigating potential threats to an application or system. Without such structure, analysing complex architecture can quickly become overwhelming. These methodologies provide a consistent framework to ensure that no key aspect of security is overlooked. Organisations may adopt a specific methodology that fits their development model, combine several, or even create their own based on operational needs. Below are some of the most widely used and recognised threat modeling methodologies
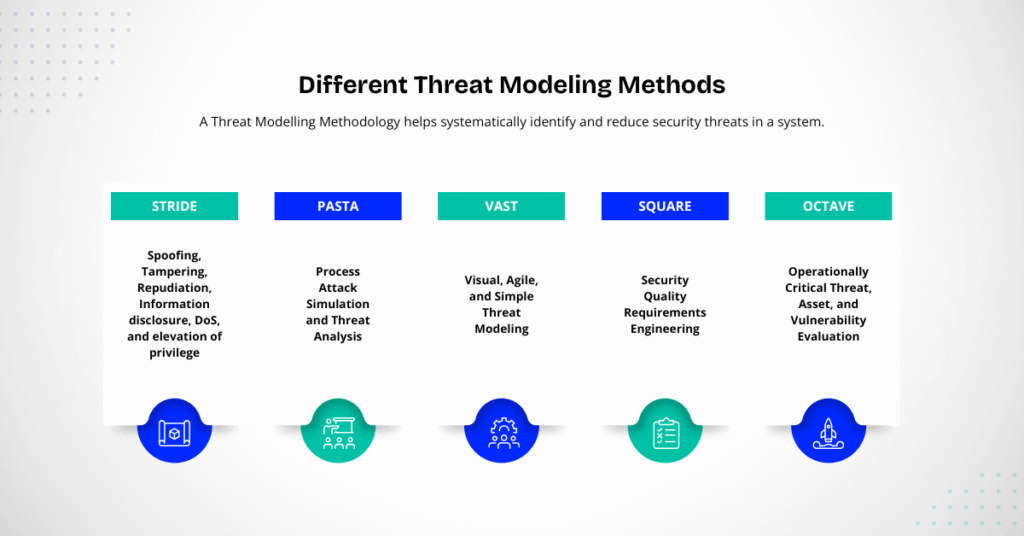
1. STRIDE
- Spoofing, tampering, repudiation, information disclosure, denial of service, elevation of privilege
- One of the most widely used and fundamental threat modeling techniques is STRIDE, which was created by Microsoft. It offers a methodical approach to classifying security threats into six major categories:
- Spoofing is the act of pretending to be a different person or system.
- Tampering is the act of changing data or code without permission.
- Repudiation: Performing activities that are not traceable or verifiable.
- Information disclosure is the act of revealing sensitive information to unapproved parties.
- Denial of Service (DoS): disrupting the system functionality or availability of a system.
- Elevation of Privilege: Having more access than is allowed.
- STRIDE helps teams in identifying specific vulnerabilities in data processing, system integrity, and authentication by comparing each part of an application to these categories. For software developers and architects, incorporating security early in the design process is quite beneficial.
2. PASTA
(Process Attack Simulation and Threat Analysis)
The goal of the risk-centric PASTA technique is to simulate actual attack scenarios. It is divided into seven specific phases, which include from business objectives establishing technical scope and business goals, identifying threats, assessing risk impact, and analyzing vulnerabilities. The methodology aligns security with business goals, ensuring that mitigation strategies protect the most critical assets. Because PASTA bridges the gap between technological vulnerabilities and business implications, it is especially useful for businesses looking for a thorough and measurable approach to risk assessment.
3. VAST (Visual, Agile, and Simple Threat Modeling)
key components of the VAST methodology are Scalability, automation, and interaction with DevOps and Agile workflows. It is often implemented using threatmodel, a commercial software program made to automate threat modeling for big and complex systems, and is frequently used to apply it. To assist teams in rapidly identifying dangers in both application and operational settings, VAST uses visualization techniques. Its main advantages are its ease of use and flexibility, which allow security evaluations to change over time in parallel with development processes. This makes it an excellent option for companies that use continuous integration and deployment (CI/CD).
4. SQUARE (Security Quality Requirements Engineering)
The main focus of the SQUARE technique is integrating security early in the software requirements. It was created by Carnegie Mellon University to help teams in identifying, categorizing and prioritizing security requirements before design and execution. SQUARE’s nine steps process emphasizes communication between developers, stakeholders, and security specialists. Early intervention lowers the cost and labor of correcting vulnerabilities from being embedded in the architecture, reducing the cost and effort of fixing them later. It is especially useful for projects that give security-by-design principles the highest priority.
5. OCTAVE (Operationally Critical Threat, Asset, and Vulnerability Evaluation)
The Software Engineering Institute at Carnegie Mellon created OCTAVE, which focuses on organizational risk assessment rather than just application-level threats. To evaluate an organization’s total risk posture, it assesses vital assets, the risks they pose, and current security procedures. OCTAVE empowers teams to make well-informed risk-based decisions and is suitable for businesses that see security from a management-oriented, strategic viewpoint rather than only a technical one.
Continue Reading grc-tools-for-risk-management-and-compliance
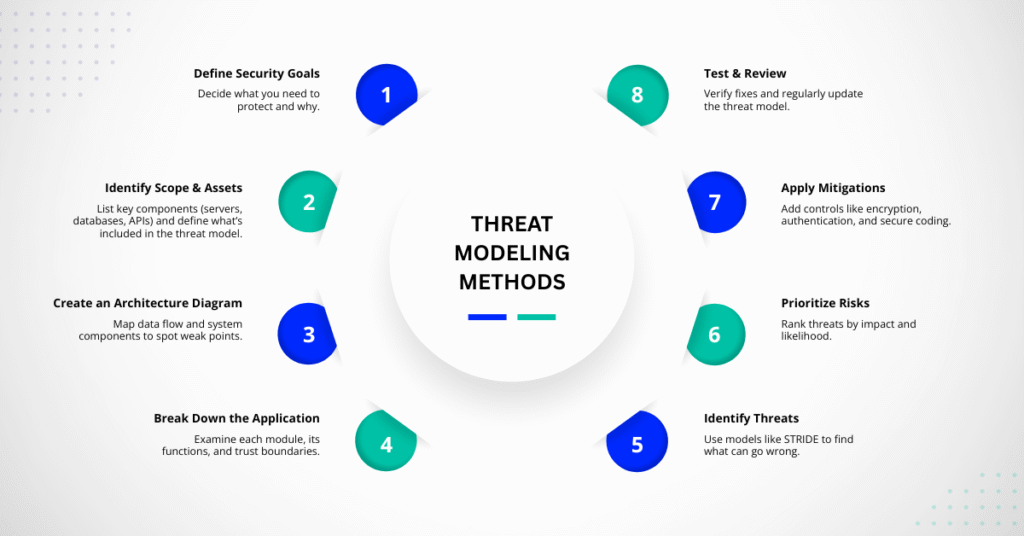
Threat Modeling Methods
Developers and security experts can identify and address potential security problems before hackers can exploit them by using the threat modeling approach. It is a methodical strategy that examines how a system functions, potential problems, and ways to make it safer. Let’s go over each step in simple terms.
1. Define Security Goals
The first step is to decide what you want to protect and why. These goals may include safeguarding user data, safeguarding financial data, or ensuring that users can always use your system. Clear goals make it easier to stay on task and recognize the biggest challenges.
2. Identify the Scope and Assets
The next step is to figure out which system components are valuable and require protection. Databases, servers, APIs, and user data are examples of what are referred to as assets. The scope, or the components of the system you’ll include in your threat model, must also be determined. You can determine what is most crucial to safeguard and where possible hazards may be present by evaluating assets and scope.
3. Create a Diagram of Architecture
It’s time to create a basic diagram that shows how your system functions. This should include all the major parts of how data flows across all of the major components, including users, web servers, databases, and external services.These diagrams helps you and your team in visualizing the system, identifying vulnerabilities, and understanding the flow of information. You can detect, for instance, whether data is transmitted unencrypted or via insecure networks.
4. Break Down the Application
In this step, you look at each part of the application in detail to understand how it works. You divide it up into smaller components, such as communication lines, data storage, and login systems, and consider how each could be compromised. It helps in identifying hazards that might not be immediately apparent. Additionally, it assists in locating trust boundaries, or the points at which data transitions from secure to less secure areas.
5. Identify Threats
Once you understand how the system works, the next step is to look for possible threats. Ask questions like: What can go wrong here?” How could this part be attacked? To do this, many teams use a model like STERIDE, which looks for six main types of threats- denial of service, spoofing, tampering, repudiation, information disclosure, and elevation of privilege. Listing out possible threats gives you a clear picture of where the risks are.
6. Evaluate and prioritize the risks
Not every threat is equally dangerous. You rank the threats in this phase according to their probability and seriousness. A threat that could cause major data loss or system failure should be fixed first. Rating and Prioritizing risks help teams focus their efforts where it matters most, instead of trying to fix everything at once.
7. Plan and Apply Mitigations
After rating the risks, the next step is to plan and add protections to reduce or remove them. This can include using encryption, adding authentication systems, fixing insecure code, or uploading old software. Each security measure should match a specific threat. For example, if unencrypted communication is a threat, the fix could be adding TLS encryption to secure data transfers.
8. Test and Review
Lastly, you must verify that the fixes function by testing them. Penetration testing, code reviews, and security scans are some of the techniques you can employ. Threat modeling is an ongoing effort rather than a one-time event. New risks may emerge whenever you add new features or upgrade your system. Maintaining the security of your application over time can be achieved by routinely assessing your threat model.
what-is-zero-day-vulnerability-explained-with-real-world-examples
When Does Threat Modeling Take Place?
Threat Modeling should take place early in the software development lifecycle (SDLC) ideally at the design and planning stage, before the application or system goes live, threat modeling should be done. By doing it early, developers and security professionals can identify and fix weaknesses in security before coding starts, saving both time and costs. But threat modeling is a continuous process that should be reviewed at every stage of the project’s lifecycle.
Here is how it fits into different stages of development:
1- During the design phase: The best time to begin threat modeling is during the design phase. The architecture and data flow of the system are currently being planned, which facilitates the visualization of potential dangers and the application of security measures prior to implementation. Early design-level defect fixes are far less expensive than post-deployment fixes.
2. During Development: Developers should update the threat model to reflect for changes to the architecture or code as new features are implemented. This ensures that freshly added components won’t create new vulnerabilities.
3. During Testing: Threat modeling is reviewed throughout testing to confirm the effectiveness of mitigations. Similar to penetration testing, security testing verifies whether the dangers that have been detected are appropriately addressed and whether any new risks have emerged.
4.After Deployment As part of continuous maintenance and security monitoring, threat modeling should continue even after an application goes live. The model should adapt to new dangers that may arise as software is upgraded, integrated with other systems, or exposed to new settings (such as cloud or mobile).
Why is Threat Modeling critical to Modern Cybersecurity?
Threat modeling is essential to modern cybersecurity because it helps businesses keep ahead of possible threats in today’s complex digital environments. Reacting after a threat arises is no longer sufficient as systems become more interconnected through cloud services, APIs, IoT devices, and third-party integrations. Threat modeling allows teams to proactively find and address security flaws before attackers can take advantage of them.
By following a structured and repeatable framework organizations can map out how their systems operate, including data flows, user access points, and communication pathways. This makes it easier to spot hidden vulnerabilities that might otherwise go unnoticed. Using tools and scoring systems like the Common Vulnerability Scoring System (CVSS). Teams can rank which problems to address first by rating risks. This ensures that limited resources are concentrated on the biggest threats rather than being dispersed over little problems.
Continue Reading what-is-six-sigma-green-belt-meaning
Core advantages of Threat Modeling
1. Early Detection of Security Risk
One of its biggest benefits of threat modeling is that it allows teams to find potential security issues-before the application or system goes live. Developers can find weak points and address them before they become expensive issues by examining the architecture and data flow during the design process. In addition to saving time and money, this proactive strategy guards against security breaches that can endanger users or damage the company’s brand.
2. Better Understanding of System Architecture
Threat modeling gives development and security teams a clear view of how their system functions, including data flow, user access, and external connections. The visibility helps uncover hidden dependencies and trust boundaries where sensitive data may be at risk. Understanding the system’s structure also makes it easier to make smart design choices and apply security measures more effectively.
3. Improved Risks Prioritization
Not all threats are equally dangerous. By using frameworks like STRIDE or CVSS, teams can prioritise risks according to their impact, likelihood, and severity by using threat modeling. Organisations can determine which dangers require immediate attention and which can wait. This ensures that scarce security resources are directed toward high-risk areas that have the potential to do the most harm.
4. Strengthened Application and Network Security
By identifying and fixing vulnerabilities early, organisations can build stronger applications and secure systems. Threat Modeling encourages the use of practices like encryption, access control, and secure communication channels. Over time, this leads to a more resilient infrastructure that is harder for attackers to exploit.
5. Time and Cost Efficiency
Fixing a security flaw during the design phase costs far less than fixing it after deployment or during a cyber incident. Threat Modeling reduces long-term costs by preventing last-minute fixes, downtime and potential time by allowing teams to plan security measures early, instead of reacting to problems later.
6. Enhance Communication Between Teams
Threat modeling encourages collaboration between security teams, developers, and architects. Teams develop a common understanding of security objectives and roles by cooperating to recognise and address possible threats. This improves communication, clarifies misunderstandings, and develops an organisation-wide “security-first” mindset.
7. Ongoing Security Improvement
Cyber threats change continuously, and Threat modeling supports an ongoing cycle of improvement. As systems evolve or expand, it is ensured that new risks are identified and reduced by routinely updating the threat model. As a result, the organisation’s defences remain solid yet adaptable enough to meet new challenges.
FAQ’s
What’s the main purpose of Threat Modeling?
Threat Modelling is a structured security exercise called threat modeling that is used to find, evaluate, and fix possible weaknesses in an application, system, or infrastructure. It involves creating a detailed representation of the system’s components, data flows, and interactions to identify potential vulnerabilities that an attacker can exploit.
When should Organisation perform Threat Modeling?
Ideally, Threat Modeling should take place during the design and planning of the application. It can, however, also be performed during development, before deployment, after major updates, or at any time when big architectural changes take place. Evolving threats are constantly managed because of ongoing threat modeling.
Which threat modeling techniques are commonly used?
The threat modeling process is guided by a number of popular methodologies. STRIDE, PASTA, VAST, SQUARE, and OCTAVE are the most widely used. Organizations select the structure that best suits their environment and goals since each offers a distinct framework, with some concentrating on system behavior and others on risk analysis or security requirements.
What are the benefits of using Threat Modeling in cybersecurity?
Threat modeling improves risk prioritization, security architecture, and business, engineering, and security team communication. Additionally, it supports compliance requirements, enhances incident response readiness, and supports businesses in early vulnerability detection. In the end, it creates a cybersecurity posture that is more solid and proactive.
Conclusion
Threat Modeling has become an essential practice for organisation,aiming to build systems that are safe, reliable, and prepared for the future. Teams obtain the clarity required to make more intelligent security decisions by methodically identifying assets, evaluating architecture, detecting threats, and ranking risks. Businesses can select the strategy that best fits their environment and maturity level from a variety of tried-and-true approaches, including STRIDE, PASTA, VAST, SQUARE, and OCTAVE. Above all, threat modeling is a continuous process that changes as threats, technologies, and architectures do. It improves security posture, reduces vulnerabilities, promotes compliance, and ensures that businesses stay one step ahead of cybercriminals when used regularly and collaboratively.





