Preventing data breaches is the best defense against the expense and nightmare that they bring. However, you need to know them before you can stop a data breach. The sorts of data breaches, their costs, and how to avoid them are all covered in the straightforward guide below, which is intended for small- to medium-sized business owners. Strong security procedures must be implemented by enterprises in order to stop data breaches. Implementing multi-factor authentication and secure passwords should be the first step. Patch vulnerabilities in software by updating it frequently. When sensitive data is in transit. Keep an eye out for odd activity on systems and restrict user access according to duties.
Table of Contents
How do Data Breaches happen?

Top 10 Biggest Data Breaches of all Times
When hackers gain access to sensitive data, data breaches occur. The cost of these breaches is extremely high.According to IBM’s 2020 Cost of a Data Breach Report, in addition to the irreversible harm to the company’s reputation, the average overall cost of a data breach is $3.86 million. It costs time, too. IBM discovered that it takes 280 days on average to find a breach and successfully contain it.
From incident response teams to artificial intelligence, there are numerous high-level security measures you may implement to stop a data breach. It is important to understand how breaches happen if you are a small business owner or just want to know what you can do to avoid them.
Physical Action
Although you might believe that cybercriminals are skilled hackers who can only access data online, they might also gain access through physical means. They might steal documents, computers, phones, or storage devices, for instance. Additionally, they might copy tangible things without anyone noticing. Even discarded documents or hardware can leak sensitive data if not destroyed properly. To prevent such breaches, organizations should secure physical access, train employees, encrypt devices, and safely dispose of confidential materials. Physical security is a vital part of any complete cybersecurity strategy.
Social engineering
An effective data breach prevention strategy includes safeguarding your company from online security risks. You’ve undoubtedly heard of phishing, which is the practice of cybercriminals sending phony emails to obtain private information.
For example, they could send an email claiming to be from the IT department of your business asking for a staff member’s password to be changed so they can access their accounts. These frauds, which can take the shape of phone calls or emails, give con artists access to private data that they can either sell or use to conduct fraud.
Human error
Malicious action isn’t necessarily the cause of data breaches. In actuality, hostile assaults account for only over half (52%) of breaches, according to IBM. Data breaches are not always the result of malicious activity. According to IBM, hostile attacks actually only make up more than half (52%) of breaches. About half of breaches are the consequence of carelessness or unintentional activities, with hostile attacks accounting for 52% of breaches, according to IBM. To lessen the risks brought on by human error, regular training, unambiguous security policies, and error-proof solutions are crucial.
Also read data-breach-laws-and-regulations-to-know to know more about Data Breach.
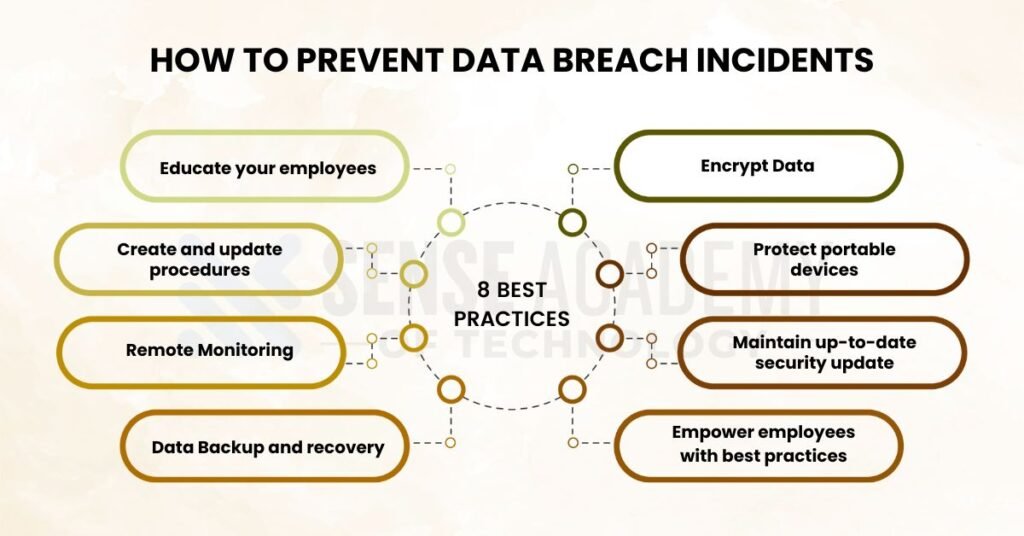
How to prevent Data Breach incidents: 8 Best practices
It’s crucial to spend time and money preventing data breaches because they can be very expensive. As a small business owner or individual employee, you can follow these 12 best practices to prevent data breaches.
1.Educate your employees
One of the best ways to stop data breaches is to fight ignorance. It’s critical to teach your staff how to prevent data breaches. This can be achieved by teach employees how to make secure passwords, how frequently to update them, and how to recognize, and report phishing scams and other questionable activities.
2.Create and update procedures
You can develop and regularly update procedures according to data security requirements. This will make it obvious what data-related expectations your firm has. Additionally, it will remind your staff that you take data seriously and demonstrate to them that they should do the same. Regarding access to specific kinds of data, it is also advisable to think about utilizing roles and permissions. PaySimple, for instance, allows you to assign users different levels of access and viewing privileges. This function offers a proactive method of implementing data operations in your company.
SIEM Tools Comparison: Best for Detecting Data Breach Activities
3.Remote Monitoring
A proactive approach to cybersecurity, remote monitoring makes sure your systems are always monitored for indications of attacks, malfunctions, or odd activities. Businesses can collaborate with managed IT service providers, who employ cutting-edge technologies to identify and address problems immediately, as an alternative to employing a full-time, internal IT staff. This reduces downtime and improves security while also saving money. Remote monitoring keeps your network secure, effective, and ahead of possible threats with real-time warnings and professional supervision.
4.Data Backup and recovery
To safeguard your company from unplanned data loss due to cyberattacks, system malfunctions, or natural catastrophes, data backup and recovery are crucial. A reliable backup system minimizes downtime and guards against permanent loss by guaranteeing that important files can be promptly recovered. To be as secure as possible, backups should be saved locally and in the cloud, be automatic, and be encrypted. Testing recovery procedures on a regular basis to make sure they function when required is equally crucial. A robust backup and recovery plan ensures the safety and resilience of both your company and your data.
5. Encrypt Data
One of the best strategies to prevent unwanted access to sensitive data is to encrypt it. By transforming data into unintelligible code that can only be viewed with the right decryption key, encryption makes sure that even in the event that data is intercepted, attackers cannot utilize it. This holds true for both data in transit (transmitted via networks or email) and data at rest (stored on devices or servers). Make sure your Wi-Fi is concealed from the public and protected using robust encryption, such as WPA3. To prevent Wi-Fi vulnerabilities for extremely critical processes, think about utilizing cable connections or secure VPNs.
5 Stages of a Data Breach and How to stop each one
6. Protect portable devices
If not properly secured, portable electronics like USB drives, cellphones, and tablets pose a significant security risk since they are vulnerable to theft or loss. Employing biometric locks or strong passwords, as well as full-device encryption, will help protect them. In the event that the device disappears, install reliable anti-theft apps that enable remote tracking, lockout, or data wiping. Keep clear of storing extra sensitive information, and make sure the software on the gadget is up to date. Limiting Bluetooth or public Wi-Fi automatic connections also lowers the possibility of unwanted access.
7. Maintain up-to-date security update
Keeping security software updated is a vital line of protection against current online threats. Because hackers are always changing their strategies, your systems may be vulnerable to attacks using outdated software. Use firewalls, antivirus software, and anti-spyware programs in tandem to guard against malware, data theft, and illegal access. To guarantee that your program is always up to date with the newest security patches and threat definitions, enable automatic updates. Run real-time scans with these tools to ensure ongoing security. Working with a reputable cybersecurity supplier will guarantee correct setup, ongoing monitoring, and quick reaction to any threats for the best results.
8. Empower employees with best practices
Employees should be well-versed on websites that pose a risk to work computers, such as file-sharing websites. The same is true of the mobile devices people use for work.
Encourage them to keep other activities on their own computers and to use work computers exclusively for business purposes, especially if they work remotely.
FAQ’s
For what reasons do data breaches target small businesses?
Attackers can more easily target small organizations because they frequently lack sophisticated cybersecurity safeguards. With little opposition, hackers view them as gateways to more extensive networks or important data.
How regularly ought we to perform data backups?
Data should ideally be backed up every day, with real-time backups of vital systems. Testing backup recovery on a regular basis guarantees that, in the event that data is lost or damaged, operations can be promptly restored.
What causes data breaches the most frequently?
One of the main causes is human mistake, which includes things like phishing scams, weak passwords, and unintentional data sharing. For this reason, in addition to technical protections, personnel training and well-defined procedures are crucial.
Conclusion
In order to prevent data breaches, a security-first culture must be established, not merely technological advancements. Strong authentication, frequent upgrades, data encryption, staff training, and regular audits can all help firms significantly lower their risk. In order to maintain regulatory compliance, prevent financial loss, and preserve consumer trust, small and medium-sized enterprises must follow certain best practices. By being proactive now, you can prevent a costly breach for your company tomorrow.





