Table of Contents
What is SOC 2 Compliance?
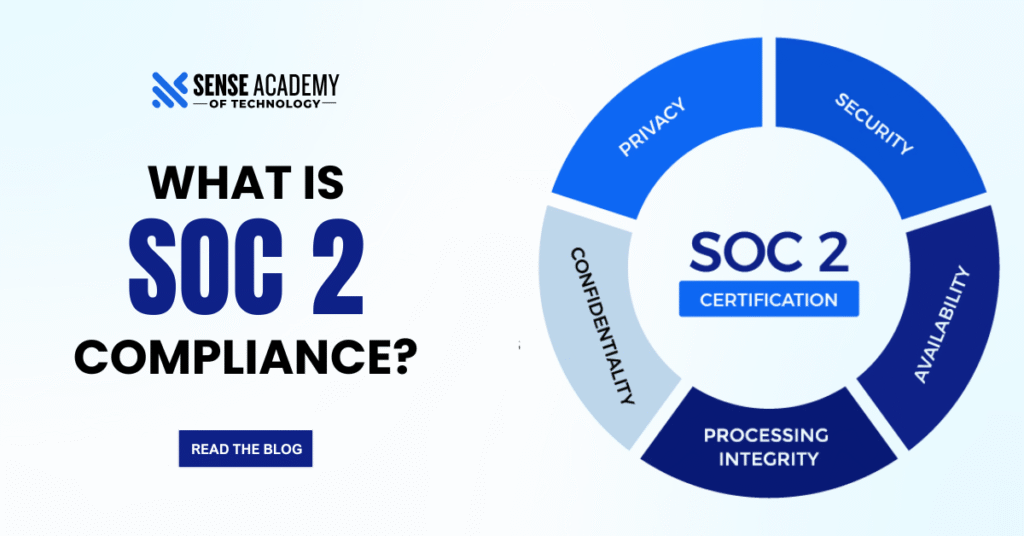
System and Organization Controls 2, or SOC 2, is a well-known compliance framework created to guarantee that service providers handle client data safely. Businesses who use technology and cloud computing find it especially important. Security, Availability, Processing Integrity, Confidentiality, and Privacy are the five Trust Services Criteria that serve as the foundation for SOC 2 audits.
Why It’s Important for IT, SaaS, and Cloud Companies
In addition to being a best practice, SOC 2 compliance gives businesses that handle sensitive consumer data, provide software, or use cloud services a competitive edge. More and more, partners and clients want evidence of robust data security and operational integrity. Reaching SOC 2 compliance shows enterprise clients that a business is dedicated to security and fosters confidence. Comprehending SOC 2 principles enhances a professional’s skill set and provides access to jobs in cloud risk management, DevSecOps, cybersecurity, and GRC.
Breaking Down SOC 2. what every cloud Professional must know about
The Trust Services Criteria, which are five fundamental principles—security, availability, processing integrity, confidentiality, and privacy—are the foundations of SOC 2 compliance. Knowing these is crucial for cloud professionals to develop systems that users and clients can genuinely trust, in addition to passing audits. These principles influence how safe, dependable, and accountable your service is, whether you’re managing infrastructure, creating SaaS platforms, or guaranteeing uptime. In today’s compliance-driven employment environment, mastering them provides you a distinct advantage.
Also visit how-to-prepare-for-aws-sap-on-aws-certification
SOC 2 Certification and who should pursue it
A cybersecurity and data privacy compliance framework created especially for technology and cloud-based businesses is called SOC 2. The American Institute of Certified Public Accountants (AICPA) created SOC 2 mainly for service firms dealing with cloud-based customer data processing or storage. It is particularly crucial for cloud infrastructure platforms, managed IT services, and SaaS providers. Despite not being mandated by law, SOC 2 accreditation is frequently a competitive requirement for businesses hoping to attract enterprise clients, particularly in regulated sectors, as they must demonstrate their ability to adequately protect customer assets.
Top Job Roles that require SOC 2 Certification
Why SOC 2 Certification matters for Cloud Professionals
SOC 2 certification is seen by cloud specialists as evidence of a company’s dedication to operational integrity and data protection. Gaining the trust of clients, fulfilling business needs, and guaranteeing safe cloud environments all depend on it. SOC 2 knowledge makes experts great assets in any cloud-focused firm by assisting in the alignment of systems with industry standards, lowering risk, and promoting compliance-driven growth.
Why SOC 2 Certification matters for SaaS Professionals
SOC 2 certification is crucial for SaaS professionals to demonstrate that client data is handled safely and consistently. It keeps a competitive advantage, wins business transactions, and satisfies customer requests. Understanding SOC 2 also enables SaaS teams to create platforms that adhere to compliance guidelines, lowering legal risks and increasing client trust.
Visit 8-best-reasons-choose-managed-security-services
How to gain SOC 2 certification and learning pathways
Start with online learning environments that provide introductory to advanced courses on risk assessment, compliance frameworks, and Trust Service Criteria if you want to learn SOC 2. These are perfect for independent study. For students and working professionals seeking more structured learning, academy programs (such as those offered by Senselearner) provide instructor-led sessions, certification preparation, and career counseling. Above all, practical laboratories and audit simulations provide you with practical experience in implementing SOC 2 controls, detecting weaknesses, and getting ready for audits. For positions in SaaS compliance, GRC, and cloud security, this hands-on experience is essential.
SOC 2 Compliance VS Certification

SOC 2 Compliance
A company that complies with SOC 2 Compliance complies to important security and privacy procedures that are based on the Trust Service Criteria (Security, Availability, Confidentiality, Processing Integrity, and Privacy). Responsible data management is an internal endeavor. Being SOC 2 compliant indicates that a business is actively adhering to industry standards in order to protect client information, control risk, and create reliable infrastructure. This entails putting in place procedural controls like staff training and incident response procedures in addition to technical controls like encryption, access control, and system monitoring. In order to safeguard data and preserve operational integrity, businesses usually evaluate and implement these standards internally.
SOC 2 Certification
It is the external validation—a formal audit carried out by a certified public accounting firm—that demonstrates your compliance to stakeholders and clients. There are 2 types of audits. Type I audit analyze the controls’ design at a particular moment in time, while Type II audits evaluate the controls’ operational efficacy over a longer time frame (often three to twelve months). An SOC 2 report, which is a formal, third-party guarantee to clients, partners, and regulators that the company’s systems are safe and compliant, is given to the business following a successful audit. Getting certified is about proving a sustained, verifiable dedication to user data protection and openness, not just about checking boxes.





